Relying on ‘Click-Ops’ for platform management inevitably results in Architectural Drift. When environments, from Sandbox to Production, are configured by hand, they become divergent and impossible to replicate. This lack of standardization triggers systemic failures:
- Manual bottlenecks and human error: DevOps research indicates that manual configuration in IT environments creates a massive surface area for error, contributing to nearly 70% of production outages
- Configuration drift and security gaps: Because environments are adjusted manually, “drift” inevitably occurs. A security patch applied to one region might be missed in other regions, leading to inconsistency. This lack of parity makes testing unreliable because environments are no longer truly identical
- The AI and API governance gap: The emergence of AI Agents and Model Context Protocol (MCP) servers introduces a complex layer of risk that traditional manual API Management (APIM) cannot handle at scale
- API instances and policies: Managing hundreds of API instances and their associated security policies (OIDC, Rate Limiting) across multiple environments becomes a “search and replace” mission leading to inconsistent security
- MCP servers: These are registered without strict tool-scoping, leaving the data-to-AI connection unmonitored
- AI agents: Without version-controlled system prompts and documented data-tool bindings, organizations face “Shadow AI” risks. The logic governing an AI’s behavior becomes undocumented and untraceable, bypassing the rigorous lifecycle management required for enterprise compliance
Unified lifecycle automation via Infrastructure-as-a-Code (IaC)
Adopting the MuleSoft Terraform Provider shifts your strategy from manual maintenance to Infrastructure-as-Code (IaC). Terraform acts as the single source of truth, managing the Data (APIs), Context (MCP), and Intelligence (Agents).
The MuleSoft Terraform Provider allows you to define your entire platform, Business Groups, Environments, and VPCs, as code. Instead of jumping between UI screens, you use a single version-controlled file as your single source of truth for repeatable deployment of infrastructure.
Key capabilities
- Unified lifecycle management: A single, version-controlled source of truth to provision, secure, and monitor the “Modern Triad”: APIs, MCP servers, and AI agents
- Infrastructure-as-Code for CloudHub 2.0: Eliminate manual networking hurdles. Automate the creation and orchestration of CH2.0 Private Spaces, VPNs, and firewall rules, moving from complex “ticket-based” network requests to instantaneous, code-driven deployments
- Automated governance and access management: Implement Identity-as-Code by automating Business Group hierarchies, Environment creation, and Teams
- Runtime-agnostic security: Define security guardrails once as Policy-as-Code (OIDC, Rate Limiting, AI Prompt Filters). Apply these guardrails universally across CloudHub 2.0 and MuleSoft Omni Gateway to ensure a zero-drift security state regardless of where the runtime lives
- Enterprise velocity at scale: Align MuleSoft with the global HashiCorp ecosystem. Reduce time-to-market by “stamping out” identical, pre-approved environments globally, bypassing the manual configuration bottlenecks that plague traditional setups
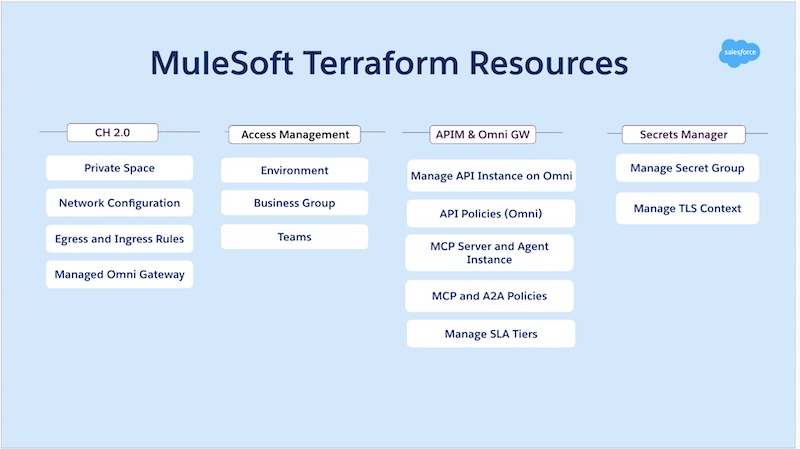
MuleSoft resources that can be managed via Terraform
| CloudHub 2.0 | Access Management | APIM and Omni GW | Secrets Manager |
|---|---|---|---|
| Private Spaces | Environment | Manage API instance on Omni | Manage Secret Group |
| Network configuration | Business group | API policies (Omni) | Manage TLS Context |
| Egress and Ingress rules | Teams | MCP server and agent instance | |
| Managed Omni Gateway | MCP and A2A policies | ||
| Manage SLA tiers |
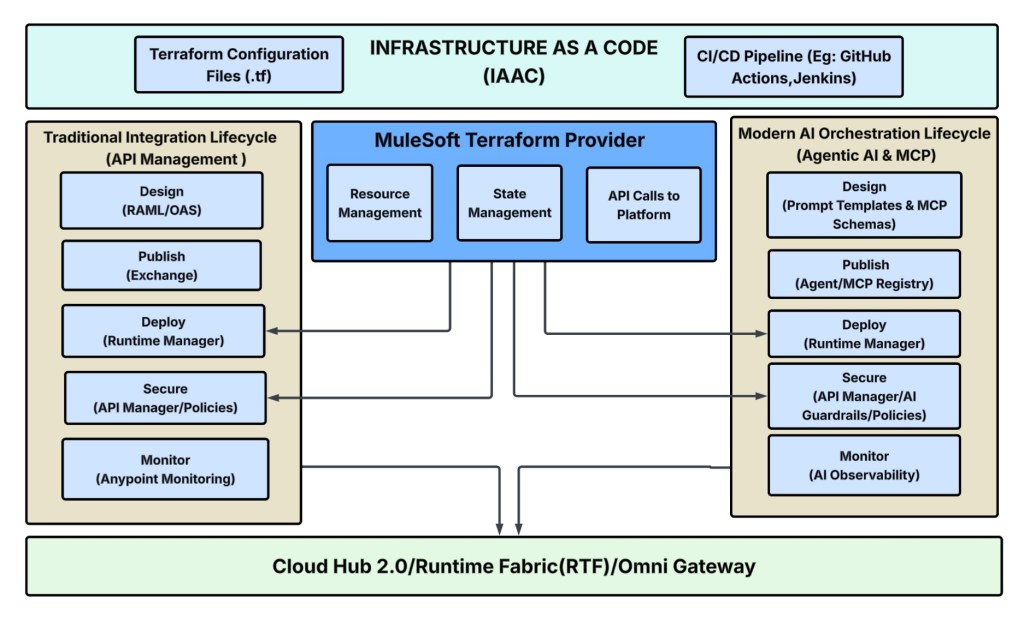
MuleSoft Terraform Provider architecture
Based on the architectural diagram below, here is how MuleSoft Terraform Provider works:
- Unified control plane: The Terraform Provider sits at the center, executing instructions from your code (.tf files) and CI/CD pipelines to automatically manage resources across the entire platform
- Synchronized lifecycles: It bridges the gap between Traditional APIs (left) and Modern AI Orchestration (right). By using a single provider, you ensure that your API security policies and your AI Agent guardrails are deployed and updated in perfect sync
- Automated runtime delivery: The provider handles the complex “handshakes” required to push configurations down to the Runtime Plane – whether you are running on CloudHub 2.0, Runtime Fabric (RTF), or Omni Gateway – eliminating manual setup and “Click-Ops” errors
Real-world use case: The “smart badge” onboarding
A global enterprise needs to automate the issuance of physical and digital badges for thousands of new hires across multiple regions. To do this securely at scale, they must unify three distinct technology layers:
- The data (APIs): A backend service that manages employee records and badge status
- The context (MCP): A Model Context Protocol server that translates complex office security rules for AI consumption
- The intelligence (AI agents): A “Badge Concierge” bot that interacts with employees to verify photos and trigger issuance
Using the MuleSoft Terraform provider, the entire regional stack is provisioned in one atomic execution. This eliminates the “Click-Ops” bottleneck where architects previously jumped between five different UI screens.
The solution: The unified terraform blueprint
The Terraform code acts as the source of truth. Instead of five different UI screens, the entire regional stack is defined in a single .tf file.
- The secure entry point (Omni Gateway): The anypoint_managed_omnigateway acts as the physical/digital bridge. It is deployed locally in each regional office (London, Singapore, New York) to ensure low latency when a new hire uploads their photo
- The smart backend (API instance): The anypoint_api_instance doesn’t just “route traffic”. It acts as the interface for the Badge Concierge
- Base path: /badge-service/v1
- Upstream: Points to the internal Employee Record System.
- Logic: By using Terraform, you ensure that the API is automatically governed by policies like JWT Validation, ensuring only authorized AI Agents can trigger a badge print
- MCP server: While not explicitly in the MuleSoft provider, Terraform allows you to provision the MCP Server (which holds the office security rules) alongside the Gateway. This ensures that when the Gateway goes live, the “intelligence” (the rules the AI follows) is already deployed and synced
Example .tf file
###############################################################################
# The Secure Entry Point (Omni Gateway)
###############################################################################
resource "anypoint_managed_omni_gateway" "badge-concierge-gateway" {
name = "badge-concierge-gateway
environment_id = var.environment_id
target_id = var.target_id
}
###############################################################################
# The Smart Backend (API Instance)
# ---------------------------------
# Acts as the interface for the Badge Concierge
# Governed by JWT Validation policies to ensure only authorized AI Agents
# can trigger badge printing
###############################################################################
resource "anypoint_api_instance" "employee_badge_api" {
organization_id = var.parent_organization_id
environment_id = var.environment_id
instance_label = "employee-badge-api"
spec = {
asset_id = var.badge_api_asset_id # Badge Service API spec from Exchange
group_id = var.parent_organization_id
version = var.badge_api_asset_version # e.g., "v1.0.0"
}
endpoint = {
base_path = "/badge-service/v1" # Public-facing endpoint
}
gateway_id = anypoint_managed_omni_gateway.badge-concierge-gateway.id
upstream_uri = "http://employee-records.internal:8080" # Internal Employee Record System
}
##########################################################################
# Badge Concierge MCP Server
# --------------------------
# MCP (Model Context Protocol) server for AI agents to interact with
# the badge issuance system securely
##########################################################################
resource "anypoint_mcp_server" "badge_concierge_mcp" {
organization_id = var.organization_id
environment_id = var.environment_id
instance_label = "badge-concierge-mcp-server"
# Exchange asset specification for the Badge MCP server
spec = {
asset_id = var.badge_mcp_asset_id # Badge MCP API spec from Exchange
group_id = var.organization_id
version = var.badge_mcp_asset_version # e.g., "v1.0.0"
}
# Endpoint configuration - base_path is used to construct proxyUri
endpoint = {
base_path = "badge-mcp/v1" # MCP endpoint path
}
gateway_id = anypoint_managed_omni_gateway.badge-concierge-gateway.id
# Backend MCP server implementation (Employee Records System)
upstream_uri = "http://employee-records-mcp.internal:8080"
}
#########################################################################
# Security Policies for Badge MCP Server
#########################################################################
# ─── 1. MCP PII Detector ─────────────────────────────────────
# Detects and protects sensitive employee data in badge requests
resource "anypoint_api_policy_mcp_pii_detector" "badge_pii_protection" {
organization_id = var.organization_id
environment_id = var.environment_id
api_instance_id = anypoint_mcp_server.badge_concierge_mcp.id
configuration = {
entities = [
"Email",
"US SSN",
"Phone Number",
]
}Now, a process that typically took two months of manual tickets and security approvals is a sub-10-minute automated deployment.
The result: Reliable scale at machine speed
By moving to a unified, automated lifecycle, organizations transform operational metrics from months to minutes:
- 80% reduction in deployment risk: Eliminating manual configuration removes the primary source of environment failure
- “Secure-by-default” environments: Every new Business Group is born with your organization’s security DNA attached. Compliance is built into the blueprint rather than being an afterthought
- Operational velocity: Provisioning a fully governed environment, complete with networking, security policies, and AI agent identities, is reduced from a days of ticket-based ordeal to a sub-10-minute automated execution
A strategic shift to operational excellence
MuleSoft Terraform Provider is more than a technical upgrade; it is a tool to activate Operational Excellence and repeatable deployments . By treating your platform as code, you gain the ability to audit changes proactively, and recover from disasters instantly. In an era where AI Agents and MCP Servers are rapidly expanding the boundaries of the application network, a declarative, version-controlled foundation is the prerequisite for success.
Achieve mathematical certainty in your governance
Move beyond manual “Click-Ops” and switch to the Official MuleSoft Terraform Provider. Ensure every regional footprint is a version-controlled, identical mirror of your security blueprint in just a few easy steps.
- Get started: Explore the HashiCorp Registry
- Deep dive: View official documentation
- See it in action: Watch the demo









