A clinician clicks “Submit prior authorization” in a care management application. That single action can trigger a chain reaction: documentation retrieval, medical policy evaluation, eligibility checks, and payer submission across multiple agents and multiple APIs.
In an agentic enterprise, that chain is where security either holds or breaks. Because the moment a workflow fans out, you want to know how to keep the clinician’s identity and intent intact across agents, tools, and downstream systems without overexposing protected health information (PHI), or granting broad, reusable credentials?
That is the core reason identity propagation matters. It’s also where Agent Fabric provides a practical, scalable answer: by enforcing identity boundaries across agent networks and governing them consistently through a unified platform.
Why identity propagation is foundational in an agentic enterprise
Agentic systems operate very differently from traditional integration patterns. Instead of a single request–response interaction, modern workflows involve:
- Planning phases, where agents decide what to do
- Execution phases, where actions are carried out across tools and systems
- Tool calls often via Model Context Protocol (MCP) and agent-to-agent coordination (A2A)
- Human-in-the-loop checkpoints that pause and resume execution
This architecture is powerful, but it moves execution closer to your most sensitive surfaces: EHR reads, clinical summaries, medication histories, payer APIs, and patient demographics. If identity is not propagated correctly, systems compensate in unsafe ways: by falling back to shared service credentials, reusing over-scoped tokens, and embedding identity hints inside payloads or agent context.
In the healthcare industry, these failures surface quickly as audit gaps, over-privileged access, and compliance risk. Identity propagation is the control that prevents those outcomes.
Identity, context, and authority must be separated
A critical principle in agentic architectures is the separation of identity, context, and authority.
Identity answers who initiated the action. Context explains why the action is happening.
Authority defines what is allowed right now. Agents reason primarily over context. Platforms must enforce authority.
When these concerns blur, authority tends to stick to context. Agents accumulate access incrementally, and security degrades without obvious failures. A sound architecture allows context to flow freely between agents while authority is continuously constrained and re-evaluated at system boundaries.
Why healthcare amplifies identity risk
Speaking about the field realities, Vara Imandi, product leader at MuleSoft says:
The truth of healthcare workflows that already span complex ecosystems: clinician-facing applications, EHR platforms, FHIR APIs, payer services, and external partners. Agentic automation multiplies the number of interactions. Agents retrieve data, apply rules, generate summaries, and coordinate across systems.
Each step introduces a new identity handoff. At each handoff, two things must remain clear: who initiated the action and which system executed it. If either becomes ambiguous, security and auditability suffer.
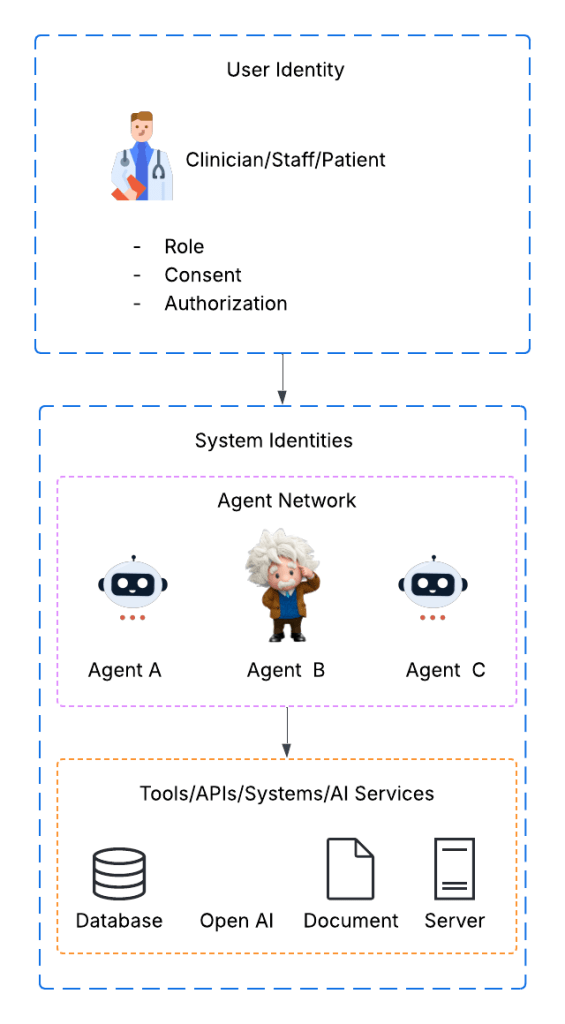
Two identity planes in an agent network
To manage this complexity, identity must be understood across two distinct planes.
Diagram 1: User identity vs. system (agent) identity
User identity explains why access is allowed. System (agent) identity explains how work is executed. A secure agentic architecture preserves both identities end-to-end without collapsing them into a single credential.
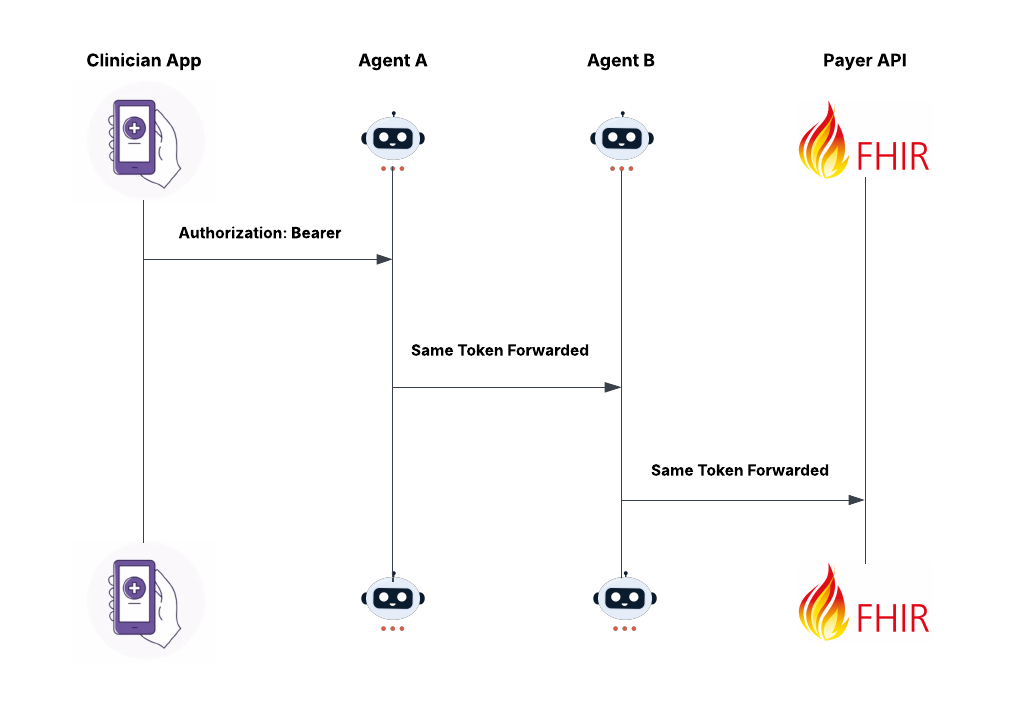
Where early agent architectures fail
Many early agent implementations attempt to preserve user context by forwarding the same access token across agents and APIs.
Diagram 2: Token forwarding anti-pattern
This approach fails at scale. Access tokens are issued for specific audiences. When reused across agents, permissions expand implicitly. Downstream systems lose the ability to enforce least privilege, and tokens often appear in logs, traces, or agent memory. As agent networks grow, the blast radius of a single token grows with them.
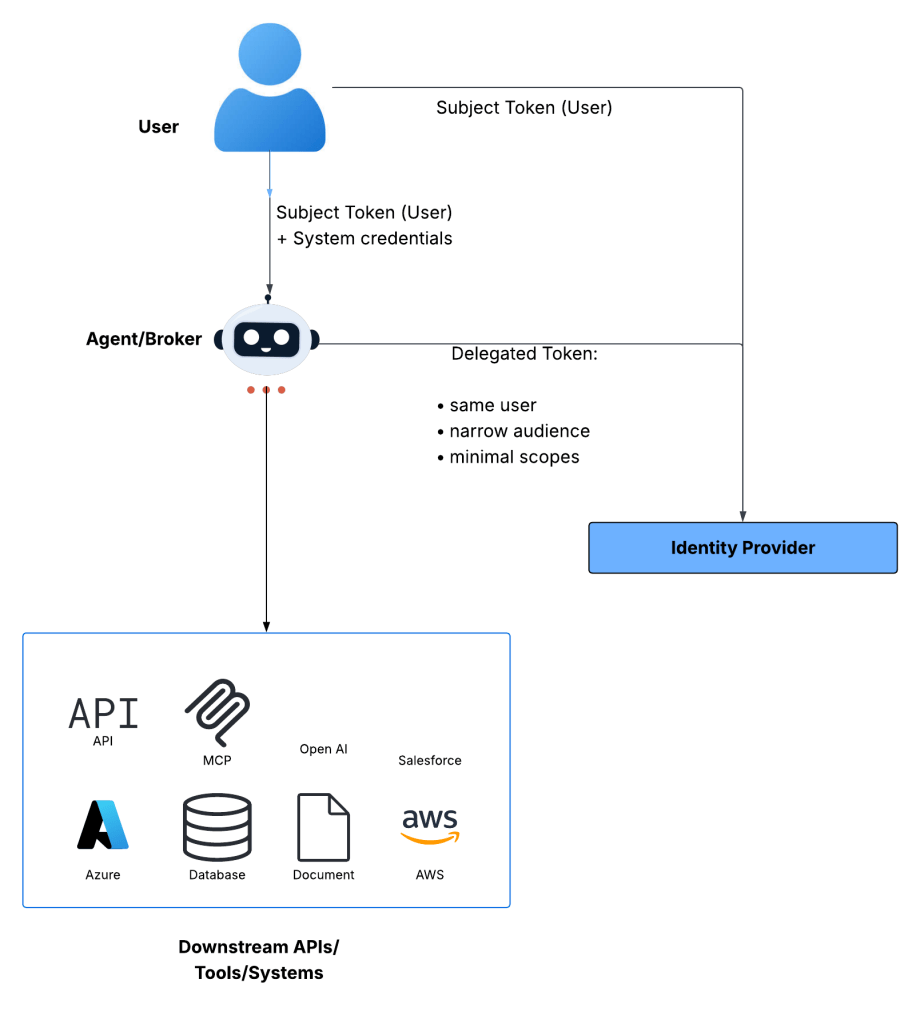
Delegated authority instead of shared credentials
Agentic systems require delegated authority, not shared credentials. Rather than forwarding a user token, the platform exchanges it for a new token that preserves the user as the subject, represents the acting system, is scoped to a specific downstream resource, and is short-lived.
Diagram 3: Delegated authority via token exchange
Each hop receives only the authority it needs, when it needs it, with clear attribution. This model aligns naturally with modern agent patterns, including planning versus execution, tool invocation, agent-to-agent collaboration, asynchronous workflows, and human approvals.
Where identity should live in modern agent systems
Access tokens belong at the transport layer, not inside agent payloads or reasoning state. Agent payloads are frequently logged, persisted, replayed, or passed into planning contexts. Embedding tokens there increases the risk of accidental exposure.
Transport-layer identity allows gateways to validate, exchange, and audit identity consistently. When tools require user identifiers, those identifiers should be minimal and treated as untrusted unless backed by token claims.
Why MuleSoft Agent Fabric fits identity-centric agent architectures
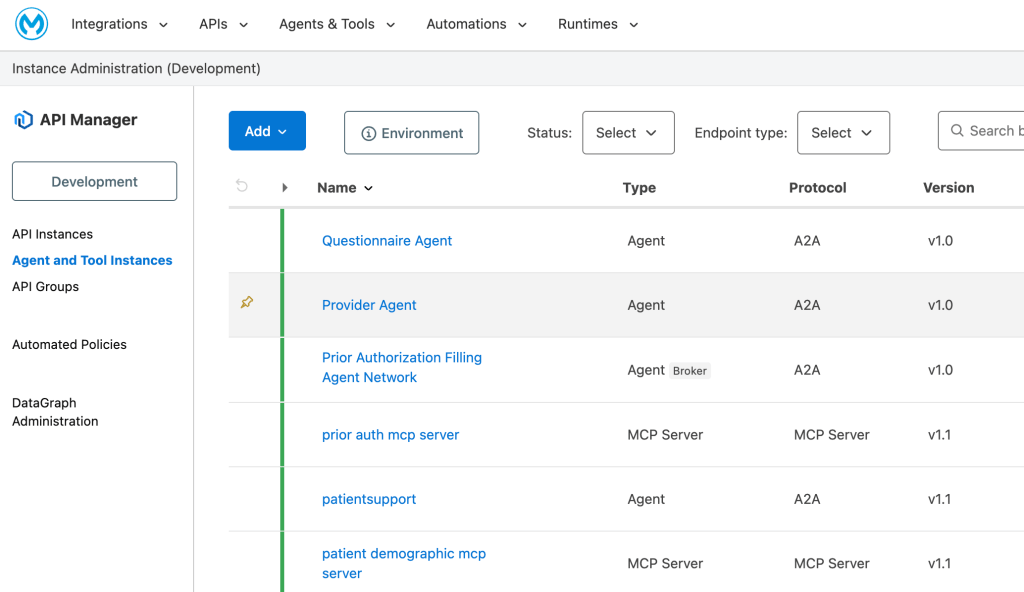
Implementing delegated authority consistently across autonomous agents is where many designs struggle. MuleSoft Agent Fabric addresses this with a brokered, policy-driven execution model built around explicit ingress and egress boundaries. Identity enforcement is centralized at those boundaries rather than embedded inside individual agents.
Diagram 4: Agent Fabric identity enforcement model
Agents focus on reasoning and orchestration. Gateways enforce identity and authority.
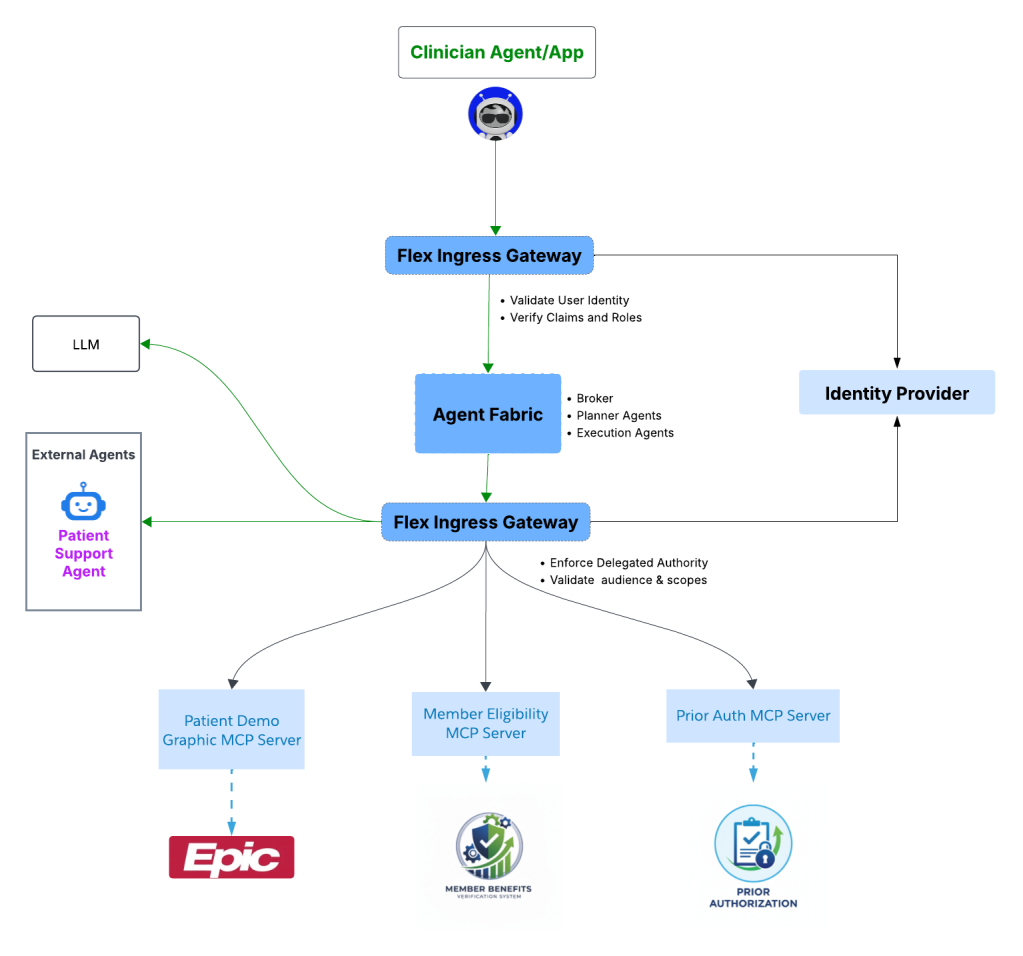
API Manager and Flex Gateway as the control plane
Agent Fabric builds on MuleSoft’s unified platform. API Manager defines authentication, authorization, audience, and scope policies centrally. Flex Gateway enforces those policies at runtime – both when traffic enters the agent network and when it leaves.
Diagram 5: Centralized governance
Security becomes policy-driven rather than code-driven, allowing governance to evolve as agent networks grow.
Extending identity controls with custom policies
Healthcare environments often require controls beyond standard OAuth validation. Flex Gateway supports custom policies using WebAssembly, enabling teams to enforce healthcare-specific rules at the gateway layer. Examples include stricter audience validation, purpose-of-use enforcement, step-up approvals, or sensitive data inspection and redaction. These controls evolve independently of agent logic.
Observability: Identity propagation must be provable
Security without observability is incomplete. Agent Visualizer provides a graph view of agent interactions, showing how agents, tools, and systems connect at runtime. Distributed tracing adds request-level detail, capturing how identity propagates and where delegation occurs. Together, visualization and tracing turn identity propagation into evidence, not assumption.
Prior authorization without identity drift example
A clinician submits a treatment request. Identity is validated before the request enters the agent network. A planning agent determines required steps. Execution agents gather documentation. Before calling the payer API, the platform enforces a payer-scoped delegated token. Throughout the workflow, identity remains intact, authority remains constrained, and access to PHI is traceable.
Why this approach aligns with healthcare compliance
Across Agent Fabric, API Manager, Flex Gateway, Agent Visualizer, and tracing: identity is explicit, authority is delegated, policy is enforced at boundaries, and behavior is observable and auditable. Security becomes a platform capability, not a workflow-by-workflow concern.
Identity propagation is how agentic healthcare scales safely
Agentic systems introduce autonomy, speed, and scale, but also new ways for identity to drift. When identity is validated at ingress, delegated through exchange, constrained at egress, and traced end-to-end, agentic healthcare systems remain governable. That is the role of MuleSoft Agent Fabric: enabling identity-safe agentic workflows that scale innovation without scaling risk.









